AuditMaster
Know Who's Doing What to Your Data, When, Where and How
Database access control is never enough because it provides no protection from accidental errors or intentional fraud. Accountability without an audit is difficult to prove and recovering from fraud without an audit is nearly impossible and always expensive. AuditMaster makes both simple without requiring changes to the code or database. Businesses can get data access security and accountability quickly, easily, and with very low maintenance overhead.
Key Benefits
- Reduce risk of fraud
- Better diagnostics and support
- Easily demonstrated accountability
- No application or database changes required
- Fast implementation and low maintenance
Ensuring Application Security
The cost of a security failure can be huge. Fraud, unauthorized access to key business files, identity theft and simple user error are all examples of security failures affecting businesses. The time and expense required to repair the damage and the costs of customer dissatisfaction and revenue loss make an audit function essential in today’s business applications. Whether the goal is reducing the risk of misuse and minimizing the effects of fraud or meeting increased expectations for security and privacy, businesses need to know what’s happening with their data.
- Detailed Audit Trail
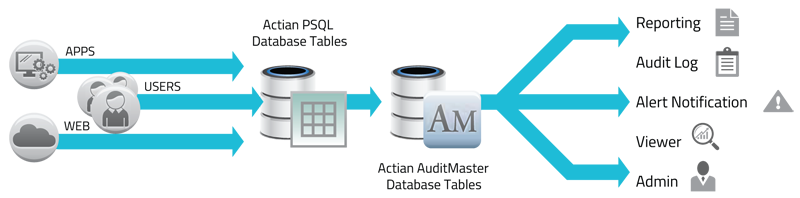
- Actian AuditMaster logs database events such as user ID, network station ID, time and date of operation, application name, database name and table type. It also logs before and after transaction images for all updated records.
- No Change to the Application
- Actian AuditMaster operates as part of the Actian Zen/PSQL database, which means adding audit capability to existing applications requires no code changes. Because it’s installed within the Actian Zen/PSQL database, Actian AuditMaster is application independent and can monitor several applications and identify the original source of each database event in the audit trail.
- Query and Alert Capability
- Actian AuditMaster includes a GUI for querying audit trail data, enabling customers to verify past activities, analyze patterns and trends, or supply evidence of compliance with security policy. Administrators and developers can also create alerts customized to their business rules. Alerts provide notice of specific events including creating, reading, updating and deleting data and can take the form of email, call to another application, or the startup of a new application.
- Support Diagnosis and Data Recovery
- Reviewing a log of database events can be a quick way to determine how an application got into a problem state. Since before and after images are stored for all changes, database rollback and fine-grain point in time recovery are possible by undoing changes captured in the audit trail.
Southdown House Software Limited Cookie Policy
We have placed Cookies on your computer/device to help make this site better. You can find out more about what cookies we use, how we use cookies, or change your cookie settings, using our Cookies Policy page.